1. How many ways, we can install Jenkins on the server?
Ans: Jenkins can be installed on a server using several methods. Below are some common ways to install Jenkins on a server:
- Package Management: Jenkins is available as a package in many popular Linux distributions, such as Ubuntu, Debian, and CentOS. You can use the package manager (apt for Ubuntu/Debian, yum for CentOS/RHEL) to install Jenkins. For example:
- Ubuntu/Debian:
sudo apt-get install jenkins - CentOS/RHEL:
sudo yum install jenkins
- Ubuntu/Debian:
- Docker: Jenkins can also be installed using Docker, which allows you to run Jenkins in a containerized environment. The official Jenkins image can be found on Docker Hub. To run Jenkins using Docker, you can use the following command:
docker run -p 8080:8080 -p 50000:50000 jenkins/jenkins
- WAR file: Jenkins can be run as a standalone application by downloading the WAR file and running it with Java.To run Jenkins using the WAR file, you can use the following command:
- java -jar jenkins.war
- Installer Package: Jenkins also provides installer packages for Windows and macOS. You can download the installer package from the Jenkins website and run it to install Jenkins on your system.
- Cloud Providers: Many cloud providers offer Jenkins as a pre-configured image or a managed service. For example, you can use AWS, Google Cloud, or Azure to deploy Jenkins instances.
- Manual Installation: If none of the above methods are suitable, you can also manually install Jenkins by downloading the Jenkins package from the Jenkins website and following the installation instructions for your operating system.
2. What are the Scopes of Jenkins Credentials?
Ans: The scopes of Jenkins credentials refer to where the credentials can be used. Jenkins allows you to define scopes for credentials to restrict where they can be used. The available scopes are:
- Global: Global credentials are available to all jobs on the Jenkins server. They can be used in any job, regardless of the folder or project in which the job is located.
- System: System credentials are available to all jobs within a specific folder. They can be used in any job within the folder, but not in jobs outside the folder.
- Folder: Folder credentials are available only to jobs within the folder where they are defined. They cannot be used in jobs outside the folder.
- Specific: Specific credentials are available only to the specific job where they are defined. They cannot be used in any other job.
3. What are the differences between Continuous Integration, Continuous Delivery, and Continuous Deployment?
Ans:
4. Name the different types of pipelines in Jenkins?
Ans:
- Declarative Pipeline
- Scripted Pipeline
5. What happens when a Jenkins agent is offline and what is the best practice in that situation?
Ans: When a job is tied to a specific agent on a specific node, the job can only be run on that agent and no other agents can fulfill the job request. If the target node is offline or all the agents on that particular node are busy building other jobs, then the triggered job has to wait until the node comes online or an agent from that node becomes available to execute the triggered build request. As a result, a triggered job may sometimes wait indefinitely without knowing that the target node is offline.
As a result, a triggered job may sometimes wait indefinitely without knowing that the target node is offline. So, it is always the best practice to tie the jobs to a group of nodes & agents, referred to with a ‘Label’. Once a job is tied to a Label, instead of a specific node/agent, any of the nodes/agents falling under the label can fulfill a build request, when a job is triggered. This way we can reduce the overall turn-around time of the builds
6. How can you create a backup and copy files in Jenkins?
Ans: In Jenkins, you can use the built-in Backup Plugin to create backups of Jenkins configuration and data files. This plugin allows you to schedule automatic backups, manage backup retention, and restore from previous backups. Here’s how you can use the Backup Plugin to create a backup:
1. Install the Backup Plugin:
- Go to Jenkins dashboard > Manage Jenkins > Manage Plugins.
- In the Available tab, search for “Backup Plugin”.
- Check the box next to the plugin and click “Install without restart”.
2. Configure Backup Settings:
- Go to Jenkins dashboard > Manage Jenkins > Configure System.
- Scroll down to the Backup section.
- Set the Backup Directory where the backups will be stored.
- Optionally, configure other backup settings like retention days, scheduling, and include/exclude patterns.
3. Create a Backup:
- Go to Jenkins dashboard > Manage Jenkins > Backup Manager.
- Click the “Create Backup Now” button.
- Optionally, provide a description for the backup.
4. Monitor Backup Status:
- The backup process will start, and you can monitor the progress in the Backup Manager.
- Once the backup is completed, you can find the backup file in the configured Backup Directory.
Note: All jenkins files are stored in the jenkins home directory. you can copy and take the backup of this folder to do the backup of jenkins
default jenkins home directory ---> /var/lib/jenkins/7. What is the Blue Ocean?
Ans: Blue Ocean is a user interface (UI) and visual designer for Jenkins.It is designed to improve the user experience and enhance the visual representation of pipelines and their results in Jenkins.
Blue Ocean provides a more intuitive interface for Jenkins users, making it easier to create, visualize, and manage continuous integration and continuous delivery (CI/CD) pipelines. It offers features like:
- Pipeline Editor: Blue Ocean includes a visual pipeline editor that allows you to create and edit Jenkins Pipeline scripts using a drag-and-drop interface. This can be particularly helpful for users who are not familiar with writing Pipeline scripts in Groovy.
- Pipeline Visualization: Blue Ocean provides a visually appealing way to view the stages and steps of a Jenkins Pipeline. It displays the status of each stage in real-time, making it easier to identify issues and understand the progress of the pipeline.
- Personalization: Blue Ocean allows users to customize the Jenkins dashboard to display only the information they need, making it easier to focus on the most important aspects of their pipelines.
- Activity Dashboard: The Activity Dashboard in Blue Ocean provides a centralized view of all pipeline runs, making it easier to track the history and status of various pipelines in one place.
- Pipeline Metrics: Blue Ocean provides insights into pipeline metrics, such as average duration and success rate, allowing users to identify areas for improvement and optimize their CI/CD processes.
8. What could be the steps to move or copy Jenkins from one server to another?
Ans:
9. What is Artifact Archival & how to do it in Pipelines?
Ans: Artifacts are the exportable/storable/archivable results of a specific job build. This can be configured using a plugin called – Copy artifact Plugin. Based on the configured pattern, the files/directories matching the configured patterns will be archived for a Jenkins build, which can be used for future references. In the pipeline, it can be configured as follows –
archiveArtifacts artifacts: ‘output/**/*’
10. Name other continuous Integration tools other than Jenkins?
Ans: There are several other continuous integration (CI) tools available besides Jenkins. Here are a few notable ones:
- Travis CI: A cloud-based CI service that is well-integrated with GitHub and is primarily used for building and testing open-source projects.
- CircleCI: Another cloud-based CI service that supports building and testing applications across multiple platforms and languages. It integrates with GitHub, Bitbucket, and other version control systems.
- GitLab CI: Part of the GitLab ecosystem, GitLab CI is an open-source CI tool that is deeply integrated with GitLab’s version control and issue tracking features.
- TeamCity: A commercial CI tool developed by JetBrains that is known for its ease of use and support for various programming languages and build tools.
- Bamboo: A commercial CI/CD tool developed by Atlassian, Bamboo offers seamless integration with other Atlassian products like Jira and Bitbucket.
- Azure Pipelines: A cloud-based CI/CD service offered as part of Microsoft Azure’s DevOps services. It supports building, testing, and deploying applications to various platforms and environments.
- GitHub Actions: A CI/CD service provided by GitHub that allows users to automate their workflows directly from their GitHub repositories.
- Drone: An open-source CI/CD platform that supports Docker-based workflows and is known for its simplicity and ease of use.
- Buildbot: An open-source CI framework written in Python that is highly customizable and extensible.
11. What is default environment variables by Jenkins & How to introduce custom environment variables?
Ans: Jenkins automatically sets several environment variables that you can use in your scripts. The default environment variables include:
BUILD_NUMBER: The current build number, such as “153”.BUILD_ID: The current build ID, such as “2005-08-22_23-59-59” (YYYY-MM-DD_hh-mm-ss).BUILD_DISPLAY_NAME: The display name of the build, which is something like “#153”.JOB_NAME: The name of the job.JOB_BASE_NAME: The name of the job without any path or folder structure.BUILD_TAG: A string representing a unique identifier for the build.EXECUTOR_NUMBER: The unique number that identifies the current executor (among executors of the same machine) that’s carrying out this build.NODE_NAME: The name of the node where the current build is running.NODE_LABELS: The labels assigned to the node where the current build is running.WORKSPACE: The absolute path of the workspace.JENKINS_HOME: The absolute path of Jenkins home directory.JENKINS_URL: The URL of Jenkins, such as “http://localhost:8080/“.BUILD_URL: The URL of the current build, such as “http://localhost:8080/job/myjob/123/“.JOB_URL: The URL of the current job, such as “http://localhost:8080/job/myjob/“.
You can introduce custom environment variables in Jenkins using the “EnvInject” plugin. below are steps to configure this.
- Install the “EnvInject” plugin:
- Go to the “Manage Jenkins” > “Manage Plugins” > “Available” tab.
- Search for “EnvInject” and install it.
- Create an environment file:
- In your Jenkins job, go to “Configure” > “Build Environment”.
- Check “Inject environment variables to the build process” and select “Properties File Path”.
- Enter the path to the properties file. For example, “${WORKSPACE}/env.properties”.
- Define your custom environment variables:
- Create a properties file with your custom environment variables. For example,
env.properties. - Add your custom environment variables in the format:
KEY=VALUE.
- Create a properties file with your custom environment variables. For example,
- Use the custom environment variables:
- In your Jenkins job’s build script, you can access the custom environment variables like any other environment variable.
12. What is the syntax of Jenkins file?
Ans: Jenkinsfile can be written in two different syntaxes: Declarative Pipeline and Scripted Pipeline.
Declarative Pipeline Syntax: Declarative Pipeline syntax is a more structured, opinionated way of defining pipelines. It is based on the Groovy programming language and provides a more human-readable way of defining pipelines. Here is an example of a Declarative Pipeline:
pipeline {
agent any
stages {
stage('Build') {
steps {
echo 'Building the application'
}
}
stage('Test') {
steps {
echo 'Running tests'
}
}
stage('Deploy') {
steps {
echo 'Deploying the application'
}
}
}
}Scripted Pipeline Syntax:Scripted Pipeline syntax is a more flexible and powerful way of defining pipelines. It is based on the Groovy programming language and allows for more complex logic and customization. Here is an example of a Scripted Pipeline:
node {
stage('Build') {
echo 'Building the application'
}
stage('Test') {
echo 'Running tests'
}
stage('Deploy') {
echo 'Deploying the application'
}
}13. What is difference between declarative and scripted pipeline?
Ans:
| Aspect | Declarative Pipeline | Scripted Pipeline |
| Syntax | Structured and opinionated | More flexible and powerful |
| Ease of Use | Easier to read and maintain | More complex and requires deeper Groovy knowledge |
| Pipeline Structure | Divided into stages and steps, with a defined structure | More freedom in defining pipeline structure, can use Groovy syntax |
| Extensibility | Limited extensibility, but well-suited for simpler pipelines | Highly extensible, suitable for complex pipelines |
| Parallel Execution | Limited support for parallel execution | Fully supports parallel execution |
| Error Handling | Limited error handling options | Full control over error handling |
| Best Use Case | Well-suited for simpler pipelines with clear stages and steps | Suitable for complex pipelines that require greater control and flexibility |
14. What is the process of making a Multibranch Pipeline in Jenkins?
Ans:
15. How can the parameters be defined in Jenkins?
Ans:
16. Explain the ways to configure Jenkins node agent to communicate with Jenkins master?
Ans:
17. How to create a slave node in Jenkins?
Ans:
- Go to manage jenkins -> nodes
- configure the below node setting:
- Name ( jenkins-slave-agent) and choose permanent agent
- Description (used to run the build jobs)
- Number of executors (This is the number of concurrent builds the node can handle)
- Remote root directory (This is the directory where Jenkins will store workspace files on the slave node)
- Labels (Labels are used to specify where jobs can run.)
- Usage ( use this node as much as possible or only build job with label expression)
- Launch Method: (launch agents via ssh)
- click on save
- Add Credentials (Optional): If the slave node requires credentials to connect, click on “Add” next to “Credentials” and enter the required credentials. You can also choose to use an existing credentials entry if it already exists.
- Connect Slave: After saving the node, you should see it listed in the “Nodes” page. Click on the node name and then click on “Launch agent”. This will provide you with a command to run on the slave machine to connect the slave to the Jenkins master.
- Verify Connection: Once you’ve run the command on the slave machine, Jenkins should detect the new node and it should be available for use. You can test the connection by running a simple build job on the new node.
18. How to configure Docker in Jenkins?
Ans:
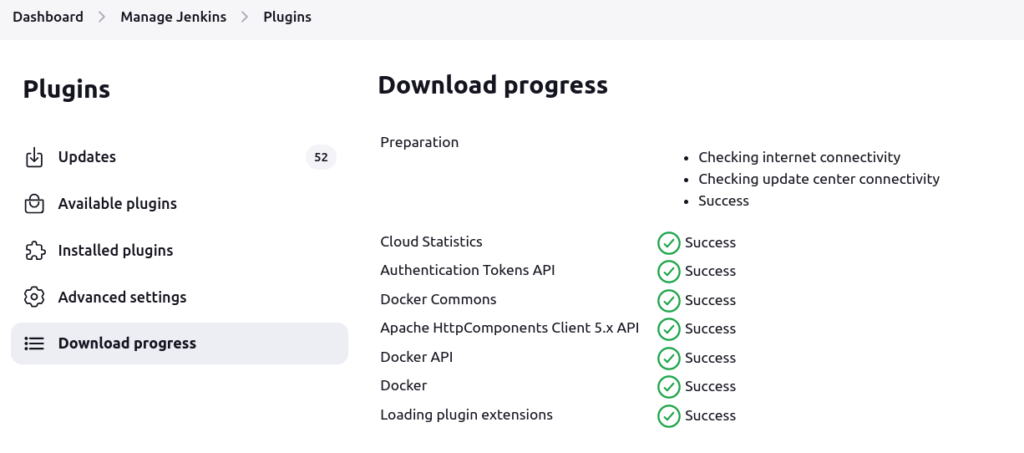
1.Install Docker Plugin: Go to manage jenkins -> plugin -> available plugin -> search docker plugin -> install without restart
2. Configure Docker in Jenkins:After installing the Docker plugin, go to “Manage Jenkins” > “Configure System”. Scroll down to the “Cloud” section and click on “Add a new cloud”. Choose “Docker” from the drop-down menu.
3. Configure Docker Host Connection: In the “Docker Host URI” field, enter the URI of your Docker host. This could be something like tcp://localhost:2375 for a local Docker host. If your Docker host requires authentication, you can enter the credentials in the “Docker Host Credentials” section.
4. Test Connection: Click on the “Test Connection” button to verify that Jenkins can connect to the Docker host.
5. Configure Docker Image: In the “Docker Agent templates” section, click on “Add Docker template”. Here, you can specify the Docker image that Jenkins will use for the build environment. You can choose an existing image from Docker Hub or specify a custom image. You can also specify additional arguments and options for the Docker container.
6. Save Changes: Once you’ve configured the Docker image, click “Save” to apply the changes.
7. Create a Jenkins Job: Now that Docker is configured, you can create a Jenkins job that uses Docker as the build environment. In the job configuration, select “Restrict where this project can be run” and choose “Docker” from the drop-down menu. You can also specify a label for the Docker agent if you have multiple Docker templates configured.
8. Run the Job: Save the job configuration and run the job. Jenkins will start a Docker container based on the specified Docker image and run the build steps inside the container.
19. How to turn off Jenkins Security if the administrative users have locked out of the admin console?
Ans: Below are some step that we can use to reset the password of jenkins:
1. Locate the Jenkins Configuration File: The Jenkins configuration file is typically located at /var/lib/jenkins/config.xml
2. Open the Jenkins Configuration File:
sudo vim config.xml3. Find the <useSecurity> Tag: Within the configuration file, look for the <useSecurity> tag. It will have a value of true or false. Change the value to false:
<useSecurity>false</useSecurity>4. Save and Close the File
5. Restart the jenkins
sudo systemctl restart jenkins6. Access Jenkins Admin Console: Once Jenkins has restarted, you should be able to access the admin console without being prompted for authentication.
7. Re-enable Security (Optional): After making the necessary changes, you can re-enable security by setting the <useSecurity> tag back to true in the configuration file:
<useSecurity>true</useSecurity>20. From one server to another, how do you copy or move your Jenkins jobs?
Ans:
1. Locate the Jenkins Job Files:Jenkins stores job configurations in XML files in the $JENKINS_HOME/jobs directory.The directory name corresponds to the job name.
2. Copy the Job Files:You can use tools like scp or rsync to copy the files over SSH, or you can use a USB drive or other storage media.
scp -r /path/to/job/directory user@new-server:/path/to/jenkins/jobs3. Restore Job Configuration in Jenkins: On the new server, move the copied job directory to the $JENKINS_HOME/jobs directory. Then, restart Jenkins to load the new job configurations.
sudo systemctl restart jenkins4. Verify Job Configuration: Once Jenkins has restarted, go to the Jenkins dashboard and verify that the job has been successfully copied or moved. If everything is correct, you should see the job listed in the Jenkins dashboard.
21. What is the process for securing Jenkins?
Ans:
- Setup authentication
- setup authorization
- Use HTTPS
- Limit access to jenkins
- Use Plugins and Tools
- Secure jenkins plugin
- Monitor Jenkins Logs
- Regularly update jenkins
- Set Up Authentication: Jenkins allows several methods for authentication, including its built-in database, LDAP, Active Directory, and third-party authentication providers like Google or GitHub. To set up authentication:
- Go to “Manage Jenkins” > “Configure Global Security”.
- Check “Enable security” and choose an authentication method.
- Configure the selected authentication method according to the documentation.
- Set Up Authorization: Authorization controls who can perform what actions within Jenkins. There are several methods for authorization, including matrix-based security, role-based access control (RBAC), and external systems like LDAP. To set up authorization:
- Go to “Manage Jenkins” > “Configure Global Security”.
- Under “Authorization”, choose an authorization strategy.
- Configure the chosen strategy according to the documentation.
- Use HTTPS: HTTPS encrypts traffic between the user’s browser and Jenkins, preventing man-in-the-middle attacks. To set up HTTPS:
- Obtain an SSL certificate for your domain. You can use a certificate authority (CA) or create a self-signed certificate.
- Install the certificate on your server.
- Configure Jenkins to use HTTPS. This involves editing the Jenkins startup options or modifying the Jenkins
web.xmlfile.
- Limit Access to Jenkins: Limiting access to Jenkins reduces the attack surface and prevents unauthorized users from accessing sensitive information. To limit access:
- Disable anonymous access to Jenkins. Go to “Manage Jenkins” > “Configure Global Security” and uncheck “Allow anonymous read access”.
- Restrict access to certain IP addresses or ranges using firewall rules.
- Use Plugins and Tools: Jenkins has several security-related plugins and tools that can enhance its security. Some useful plugins include:
- Role-based Authorization Strategy: Allows you to define roles and assign specific permissions to each role.
- Credentials Plugin: Manages credentials securely within Jenkins.
- OWASP Dependency-Check Plugin: Checks for known vulnerabilities in project dependencies.
- Secure Jenkins Plugins: Plugins can introduce vulnerabilities into your Jenkins installation. To secure plugins:
- Regularly update plugins to the latest versions to patch security vulnerabilities.
- Only install plugins from trusted sources.
- Monitor Jenkins Logs: Monitoring Jenkins logs can help detect security incidents and unauthorized access. To monitor Jenkins logs:
- Enable logging in Jenkins. Go to “Manage Jenkins” > “System Log” and set the log level to a suitable level.
- Use a log management solution to aggregate and analyze Jenkins logs.
- Regularly Update Jenkins: Regularly updating Jenkins to the latest version helps patch security vulnerabilities and ensures that your installation is secure.
22. What is a Ping Thread in Jenkins and how it works?
Ans: A Ping Thread in Jenkins is a background thread that periodically checks the availability of Jenkins agents (or nodes) and updates their status accordingly. These nodes can be either master nodes or slave nodes. The Ping Thread is responsible for checking if the nodes are online and available for build execution. If a node is unreachable or offline, the Ping Thread will mark it as offline in the Jenkins UI and will not schedule any builds on it until it becomes available again.
23. How do you secure sensitive data (like passwords and API keys) in Jenkins?
Ans: Securing sensitive data like passwords and API keys in Jenkins is crucial to prevent unauthorized access and data breaches. Here are several methods to secure sensitive data in Jenkins:
- Use Credentials
- Use secret text
- Use Environment variables
- Use File credentials
- Use Masked Passwords
- Use secret Management Tool
1.Use Credentials: Jenkins has a built-in Credentials plugin that allows you to securely store and manage credentials. You can use this plugin to store passwords, SSH private keys, API tokens, and other sensitive data. The credentials are stored encrypted in the Jenkins configuration file, and you can control who has access to them.
- To create a new credential, go to “Manage Jenkins” > “Manage Credentials” > “Global credentials (unrestricted)” > “Add Credentials”.
2. Use Secret Text: Jenkins allows you to use secret text variables in build configurations, which are stored securely in Jenkins and are only accessible to the build job. You can use secret text variables to store API keys, passwords, and other sensitive data.
- To use a secret text variable, go to the build job configuration, and use the “Secret text” option in the “Add Build Step” or “Add Post-build Action” dropdowns.
3. Use Environment Variables: Jenkins allows you to define environment variables in the Jenkins UI or in the Jenkinsfile. These environment variables can be used to store sensitive data like passwords and API keys.
- To define an environment variable in the Jenkins UI, go to the build job configuration, and use the “Environment Variables” section.
- To define an environment variable in a Jenkinsfile, use the
environmentdirective:
pipeline {
agent any
environment {
MY_SECRET = credentials('my-secret-id')
}
stages {
stage('Build') {
steps {
// Use MY_SECRET in the build steps
}
}
}
}4. Use File Credentials: Jenkins allows you to store credentials in a file on the Jenkins master and use them in build jobs. This is useful for storing credentials that are too large to store as environment variables or secret text.
- To use a file credential, create a new credential of type “File” and specify the file path.
5. Use Masked Passwords: Jenkins allows you to mask passwords in build logs, preventing them from being displayed in the console output.
- To mask a password, use the
maskPasswordspipeline step in a Jenkinsfile:
pipeline {
agent any
stages {
stage('Build') {
steps {
maskPasswords('my-password') {
// Build steps that use my-password
}
}
}
}
}6. Use Secrets Management Tools: If you have a secrets management tool like HashiCorp Vault, CyberArk, or AWS Secrets Manager, you can use the Jenkins HashiCorp Vault plugin, CyberArk Conjur plugin, or AWS Secrets Manager plugin to integrate Jenkins with these tools and securely manage and retrieve credentials.

